Checkm8 Exploit Opens Door to Unpatchable Jailbreak on iPhone 4S Through iPhone X
A security researcher who goes by "axi0mX" on Twitter today released "checkm8," which he claims is a bootrom exploit for iOS devices equipped with A5 through A11 chips, including the iPhone 4S through iPhone X, several iPad models dating back to the iPad 2, and the fifth-generation iPod touch and later.

This would be the first publicly released bootrom exploit since the iPhone 4 in 2010 and pave the way for a permanent, non-patchable jailbreak on hundreds of millions of affected iOS devices. Since the bootrom is read-only, Apple cannot patch this type of exploit with a software update.
The bootrom exploit has many other possibilities on affected devices, including downgrading iOS versions without SHSH blobs or APTickets, dual booting iOS, and running custom firmwares, according to
jailbreak enthusiasts.
This is significant news in the jailbreaking community, as the last bootrom exploit known as "limera1n" was released by George "geohot" Hotz nearly a decade ago for devices with A4 chips and earlier, including the iPhone 4, iPhone 3GS, the third- and fourth-generation iPod touch, and the original iPad.
Popular Stories
Apple will adopt the same rear chassis manufacturing process for the iPhone SE 4 that it is using for the upcoming standard iPhone 16, claims a new rumor coming out of China. According to the Weibo-based leaker "Fixed Focus Digital," the backplate manufacturing process for the iPhone SE 4 is "exactly the same" as the standard model in Apple's upcoming iPhone 16 lineup, which is expected to...
Key details about the overall specifications of the iPhone 17 lineup have been shared by the leaker known as "Ice Universe," clarifying several important aspects of next year's devices. Reports in recent months have converged in agreement that Apple will discontinue the "Plus" iPhone model in 2025 while introducing an all-new iPhone 17 "Slim" model as an even more high-end option sitting...
Apple typically releases its new iPhone series around mid-September, which means we are about two months out from the launch of the iPhone 16. Like the iPhone 15 series, this year's lineup is expected to stick with four models – iPhone 16, iPhone 16 Plus, iPhone 16 Pro, and iPhone 16 Pro Max – although there are plenty of design differences and new features to take into account. To bring ...
Apple is scaling back its Hollywood spending after investing over $20 billion in original programming with limited success, Bloomberg reports. This shift comes after the streaming service, which launched in 2019, struggled to capture a significant share of the market, accounting for only 0.2% of TV viewership in the U.S., compared to Netflix's 8%. Despite heavy investment, critical acclaim,...
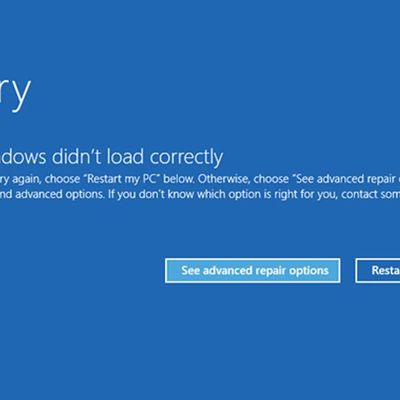
Last Friday, a major CrowdStrike outage impacted PCs running Microsoft Windows, causing worldwide issues affecting airlines, retailers, banks, hospitals, rail networks, and more. Computers were stuck in continuous recovery loops, rendering them unusable. The failure was caused by an update to the CrowdStrike Falcon antivirus software that auto-installed on Windows 10 PCs, but Mac and Linux...